SAML (Security Assertion Markup Language) enables secure, seamless access to multiple applications by exchanging authentication data between an Identity Provider (IdP) and a Service Provider (SP).
This allows users to log in once and access various services without re-entering credentials, enhancing security and user experience in enterprise environments. In this post, we’ll explore how SAML works and its benefits.
What Is Security Assertion Markup Language(SAML)?
SAML (Security Assertion Markup Language) authentication enables secure access to services by exchanging authentication and authorization data between an Identity Provider (IdP) and a Service Provider (SP). This protocol is commonly used in enterprise environments to provide users with seamless access to multiple applications using a single set of credentials.
SAML Components
Here are the key components and concepts of SAML:
- Identity Provider (IdP): This is the entity that authenticates a user and provides an assertion to the service provider. The assertion contains information about the user's identity and attributes.
- Service Provider (SP): This is the entity that receives the SAML assertion and makes access control decisions based on it. The service provider trusts the identity provider to authenticate users.
- SAML Assertion: This is the XML document that the identity provider sends to the service provider. It contains authentication information, attribute information, and authorization decisions.
- Single Sign-On (SSO): SAML is commonly used to implement SSO, allowing users to authenticate once with an identity provider and gain access to multiple service providers without re-authenticating.
- Bindings: SAML supports multiple bindings for message transport, including HTTP Redirect, HTTP POST, and SOAP.
- XML-Based Protocol: SAML uses XML to encode the messages that are exchanged between the identity provider and the service provider.
SAML 2.0
Building on the concept of SAML, let's delve into SAML 2.0, which is the most widely used version of the standard. SAML 2.0 introduced several enhancements and features over its predecessor, SAML 1.1:
- Enhanced Single Sign-On (SSO): SAML 2.0 improved the SSO capabilities, making it easier to implement and more robust in terms of security and user experience.
- Identity Federation: It allows for more seamless identity federation between different domains, making it possible for users to access resources across different organizations with a single authentication process.
- Support for Multiple Authentication Contexts: SAML 2.0 can handle different levels of authentication assurance, enabling the use of stronger authentication methods where needed.
- Metadata Exchange: This version supports the exchange of metadata between identity providers and service providers, which helps automate the configuration and establishment of trust relationships.
- Improved Protocol Bindings: SAML 2.0 includes better support for various transport protocols, such as HTTP Redirect, HTTP POST, and Artifact Binding, enhancing flexibility and compatibility.
- Attribute Query and Consent: SAML 2.0 allows for querying user attributes and managing user consent more efficiently, improving user control over personal data.
How Does SAML Authentication Work?
Authentication Process
SAML authentication begins when a user initiates the login process by entering their credentials at the IdP. The IdP verifies the user’s identity and creates a SAML assertion, which contains user attributes and authentication information.
This assertion includes details such as the user's identity, authentication time, and conditions under which the assertion is valid. To ensure the integrity and authenticity of the information, the assertion is digitally signed by the IdP.
Service Access
Once authenticated, the user attempts to access a service provided by the SP. The SP, needing to verify the user's identity, redirects the user to the IdP with an authentication request. The IdP responds by sending the SAML assertion to the SP, typically via the user’s browser using HTTP POST or HTTP Redirect.
The SP then validates the SAML assertion by checking the digital signature and the conditions of the assertion. If the assertion is valid, the SP grants the user access to the requested service. This process is seamless to the user, who only needs to log in once to gain access to multiple services.
Example Scenario
Consider a typical enterprise scenario. At the start of the workday, John logs into his company’s Identity and Access Management (IAM) system, which serves as the IdP, using his corporate credentials.
The IdP verifies John’s credentials and creates a SAML assertion, which includes information such as John’s username, authentication timestamp, and role-based access attributes. John then attempts to access the company’s hosted email service, an SP.
The email service redirects John to the IdP with an authentication request. The IdP sends the SAML assertion back to the email service via John's browser. The email service validates the assertion by checking the digital signature and ensuring that all conditions are met, such as the assertion being intended for the email service and not expired.
Once validated, John is granted access to the email service without needing to re-enter his credentials, allowing him to use the service seamlessly.
Benefits of SAML Authentication
By integrating SAML authentication, organizations can streamline user access management, enhance security by reducing the risk of password fatigue and reuse, and provide users with seamless access to multiple applications. This integration ultimately improves both operational efficiency and security posture.
What is a SAML Assertion?
A SAML Assertion is an XML document that is issued by a SAML Identity Provider (IdP) and consumed by a Service Provider (SP). It contains statements about a user that both parties can trust.
The primary purpose of the SAML Assertion is to convey security information between the IdP and SP in a secure and standardized way. Here are the key components and types of statements found within a SAML Assertion:
Key Components
- Issuer: The entity that issued the assertion, typically the IdP.
- Subject: The user or entity that the assertion is about. This usually includes a unique identifier for the user.
- Conditions: Constraints and rules under which the assertion is valid, including time restrictions and audience restrictions.
- Authentication Statement: Information about the user’s authentication at the IdP, such as the authentication method and timestamp.
- Attribute Statement: A collection of attributes about the user, such as name, email address, roles, etc.
- Authorization Decision Statement: Information about the user’s access rights to specific resources.
Types of Statements
- Authentication Statement: Describes the act of authentication at the IdP, including the method used and the time of authentication.
- Attribute Statement: Contains attributes associated with the subject. For example, a user’s email address, roles, or other relevant information.
- Authorization Decision Statement: Provides information about whether a user is authorized to access a specific resource. This includes the decision (permit or deny) and the resource in question.
How Does SAML Assertion Works
- User Requests Access: The user attempts to access a resource at the SP.
- SP Requests Authentication: The SP redirects the user to the IdP for authentication.
- User Authenticates: The user provides credentials to the IdP.
- IdP Issues Assertion: Upon successful authentication, the IdP generates a SAML Assertion and sends it back to the SP, typically via the user’s browser.
- SP Validates Assertion: The SP validates the assertion, checking its integrity, the validity of the issuer, and the conditions.
- Access Granted: If the assertion is valid, the user is granted access to the resource.
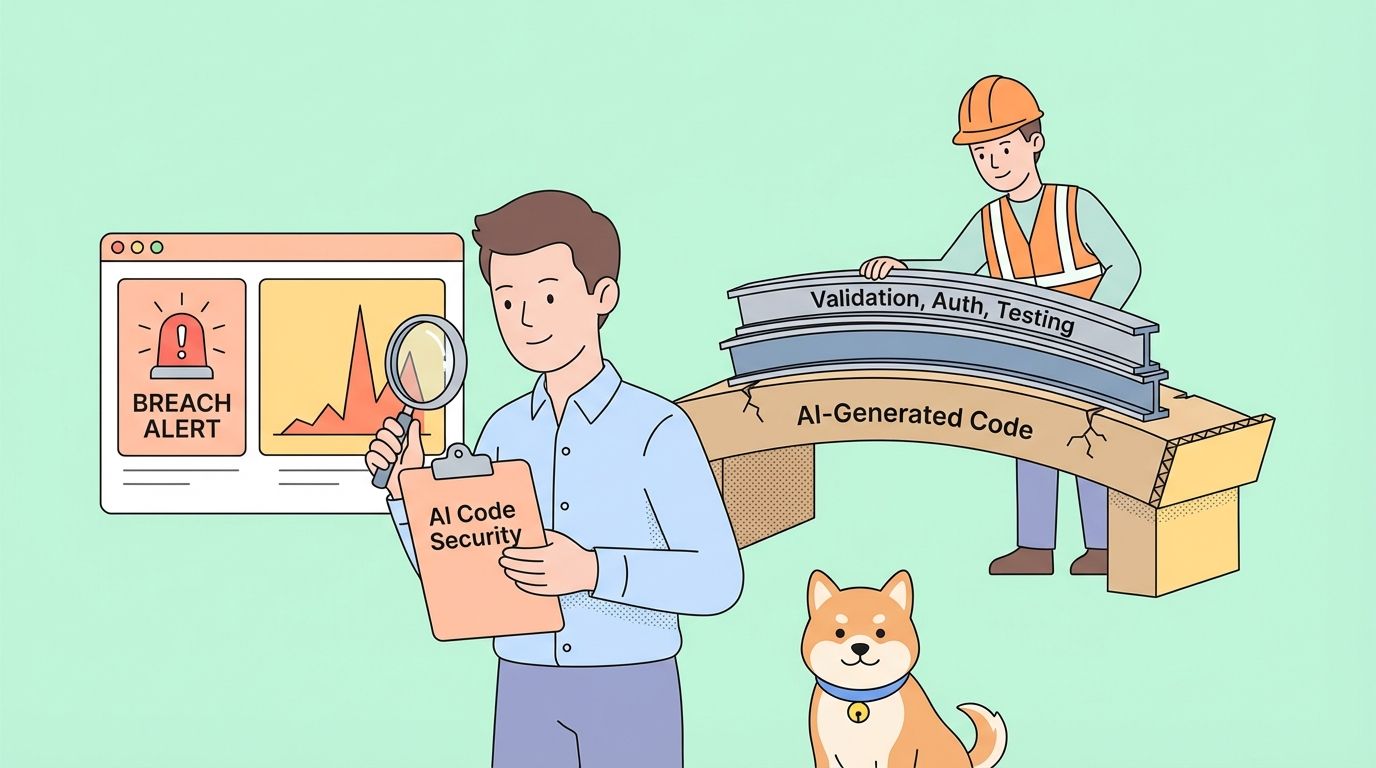
Security Considerations
- Encryption: SAML Assertions can be encrypted to ensure confidentiality.
- Signing: Assertions are often signed to guarantee their integrity and authenticity.
- Expiration: Assertions include conditions, such as time limits, to mitigate the risk of replay attacks.